[1]JIANG Hao,YAO Yuhan,WANG Jiahao,et al.Pyramid-enhanced noise-resilient watermarking for robust and high-quality image protection[J].CAAI Transactions on Intelligent Systems,2026,21(1):72-82.[doi:10.11992/tis.202507022]
Copy
Pyramid-enhanced noise-resilient watermarking for robust and high-quality image protection
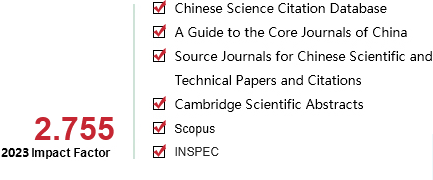
CAAI Transactions on Intelligent Systems[ISSN 1673-4785/CN 23-1538/TP] Volume:
21
Number of periods:
2026 1
Page number:
72-82
Column:
学术论文—机器学习
Public date:
2026-01-05
- Title:
- Pyramid-enhanced noise-resilient watermarking for robust and high-quality image protection
- Keywords:
- blind watermarking; information hiding; copyright protection; multi-scale features; robustness; noise attacks; end-to-end learning; deep watermarking
- CLC:
- TP391.4
- DOI:
- 10.11992/tis.202507022
- Abstract:
- To address the widespread issue of unauthorized reuse of images in digital media, robust blind watermarking is essential. However, existing methods struggle to simultaneously withstand real-world noise attacks while maintaining high extraction accuracy and excellent visual quality. To this end, we propose Pyramid-Enhanced Noise-Resilient Watermarking (PENRW), which leverages pyramid-based multi-scale feature embedding and a watermark-decoding quality enhancement module to achieve highly accurate watermark extraction under strong noise with minimal image quality degradation. Experiments demonstrate that our method surpasses current state-of-the-art approaches in both robustness and visual fidelity.
- References:
-
[1] WAN Wenbo, WANG Jun, ZHANG Yunming, et al. A comprehensive survey on robust image watermarking[J]. Neurocomputing, 2022, 488: 226-247
[2] XIAO Di, ZHAO Aozhu, LI Fei. Robust watermarking scheme for encrypted images based on scrambling and kronecker compressed sensing[J]. IEEE signal processing letters, 2022, 29: 484-488
[3] 吴嘉奕, 李晓萌, 秦川. 面向屏幕拍摄的端到端鲁棒图像水印算法[J]. 中国图象图形学报, 2023, 28(12): 3713-3730 WU Jiayi, LI Xiaomeng, QIN Chuan. Screen-shooting robust watermarking with end-to-end neural network[J]. Journal of image and graphics, 2023, 28(12): 3713-3730
[4] VAN SCHYNDEL R G, TIRKEL A Z, OSBORNE C F. A digital watermark[C]//Proceedings of 1st International Conference on Image Processing. Austin: IEEE, 2002: 86-90.
[5] DAS U K, SAMADDAR S G, KESERWANI P K. Digital forensic enabled image authentication using least significant bit (LSB) with tamper localization based hash function[C]//Intelligent Communication and Computational Technologies. Singapore: Springer, 2018: 141-155.
[6] HOLUB V, FRIDRICH J. Designing steganographic distortion using directional filters[C]//2012 IEEE International Workshop on Information Forensics and Security. Tenerife: IEEE, 2013: 234-239.
[7] KO H J, HUANG Chengta, HORNG G, et al. Robust and blind image watermarking in DCT domain using inter-block coefficient correlation[J]. Information sciences: an international journal, 2020, 517(C): 128-147
[8] LU Jianfeng, WANG Meng, DAI Junping, et al. Multiple watermark scheme based on DWT-DCT quantization for medical images[J]. J inf hiding multim signal process, 2015, 6: 458-472
[9] WANG Chunxing, LI Shang, LIU Yan, et al. Cross-scale feature fusion-based JND estimation for robust image watermarking in quaternion DWT domain[J]. Optik, 2023, 272: 170371
[10] LIU Ruizhen, TAN Tieniu. An SVD-based watermarking scheme for protecting rightful ownership[J]. IEEE transactions on multimedia, 2002, 4(1): 121-128
[11] 沈艳冰, 杨阳, 李竹. 一种适用于QR码的彩色图像数字水印算法[J]. 智能系统学报, 2020, 15(5): 949-955 SHEN Yanbing, YANG Yang, LI Zhu. Digital watermarking algorithm for color images on QR codes[J]. CAAI transactions on intelligent systems, 2020, 15(5): 949-955
[12] ZHU Jiren, KAPLAN R, JOHNSON J, et al. Hidden: hiding data with deep networks[C]//Proceedings of the European conference on computer vision. Cham: Springer, 2018: 657-672.
[13] ZHANG Honglei, WANG Hu, CAO Yuanzhouhan, et al. Robust data hiding using inverse gradient attention[EB/OL]. (2020-11-21)[2025-07-16]. https://arxiv.org/abs/2011.10850.
[14] JIA Zhaoyang, FANG Han, ZHANG Weiming. MBRS: enhancing robustness of DNN-based watermarking by mini-batch of real and simulated JPEG compression[C]//Proceedings of the 29th ACM International Conference on Multimedia. New York: ACM, 2021: 41-49.
[15] TANCIK M, MILDENHALL B, NG R. StegaStamp: invisible hyperlinks in physical photographs[C]//2020 IEEE/CVF Conference on Computer Vision and Pattern Recognition. Seattle: IEEE, 2020: 2114-2123.
[16] HUANG Jiangtao, LUO Ting, LI Li, et al. ARWGAN: attention-guided robust image watermarking model based on GAN[J]. IEEE transactions on instrumentation and measurement, 2023, 72: 5018417
[17] KOU Feifei, YAO Yuhan, HAN Jideng, et al. DualFocus GAN for robust watermarking in transportation cyber-physical systems[J]. IEEE transactions on intelligent transportation systems, 2025, 26(9): 14371-14382
[18] FERNANDEZ P, SABLAYROLLES A, FURON T, et al. Watermarking images in self-supervised latent spaces[C]//2022 IEEE International Conference on Acoustics, Speech and Signal Processing. Singapore: IEEE, 2022: 3054-3058.
[19] ZHAO Yunqing, PANG Tianyu, DU Chao, et al. A recipe for watermarking diffusion models[EB/OL]. (2023-03-17)[2025-07-16]. https://arxiv.org/abs/2303.10137.
[20] AFIFI M, DERPANIS K G, OMMER B, et al. Learning multi-scale photo exposure correction[C]//2021 IEEE/CVF Conference on Computer Vision and Pattern Recognition. Nashville: IEEE, 2021: 9153-9163.
[21] CAI Yuanhao, HU Xiaowan, WANG Haoqian, et al. Learning to generate realistic noisy images via pixel-level noise-aware adversarial training[EB/OL]. (2022-04-06)[2025-07-16]. https://arxiv.org/abs/2204.02844.
[22] WANG Baowei, SONG Ziwei, WU Yufeng. Robust blind watermarking framework for hybrid networks combining CNN and Transformer[C]//Asian Conference on Machine Learning. Hanoi: PMLR, 2024: 1417-1432.
[23] ZHU Liuhao, FANG Yixiang, ZHAO Yi, et al. Lite localization network and DUE-based watermarking for color image copyright protection[J]. IEEE transactions on circuits and systems for video technology, 2024, 34(10): 9311-9325
[24] YU F, KOLTUN V. Multi-scale context aggregation by dilated convolutions[EB/OL]. (2015-11-23)[2025-07-16]. https://arxiv.org/abs/1511.07122.
[25] CHEN L C, PAPANDREOU G, KOKKINOS I, et al. DeepLab: semantic image segmentation with deep convolutional nets, atrous convolution, and fully connected CRFs[J]. IEEE transactions on pattern analysis and machine intelligence, 2018, 40(4): 834-848
[26] COX I. Digital watermarking[J]. Journal of electronic imaging, 2002, 11(3): 414
[27] LAI C C, TSAI C C. Digital image watermarking using discrete wavelet transform and singular value decomposition[J]. IEEE transactions on instrumentation and measurement, 2010, 59(11): 3060-3063
[28] MA Rui, GUO Mengxi, HOU Yi, et al. Towards blind watermarking: combining invertible and non-invertible mechanisms[C]//Proceedings of the 30th ACM International Conference on Multimedia. New York: ACM, 2022: 1532-1542.
[29] ARAB M A, GHORBANPOUR A, HEFEEDA M. FlexMark: adaptive watermarking method for images[C]//Proceedings of the ACM Multimedia Systems Conference 2024 on ZZZ. New York: ACM, 2024: 56-66.
[30] JADERBERG M, SIMONYAN K, ZISSERMAN A. Spatial Transformer networks[EB/OL]. (2015-06-05)[2025-07-16]. https://arxiv.org/abs/1506.02025.
[31] ZHANG R, ISOLA P, EFROS A A, et al. The unreasonable effectiveness of deep features as a perceptual metric[C]//2018 IEEE/CVF Conference on Computer Vision and Pattern Recognition. Salt Lake City: IEEE, 2018: 586-595.
[32] LIN T Y, MAIRE M, BELONGIE S, et al. Microsoft COCO: common objects in context[C]//Computer Vision – ECCV 2014. Cham: Springer International Publishing, 2014: 740-755.
[33] AGUSTSSON E, TIMOFTE R. NTIRE 2017 challenge on single image super-resolution: dataset and study[C]//2017 IEEE Conference on Computer Vision and Pattern Recognition Workshops. Honolulu: IEEE, 2017: 1122-1131.
[34] TAN Weiren, CHAN C S, AGUIRRE H E, et al. Improved ArtGAN for conditional synthesis of natural image and artwork[J]. IEEE transactions on image processing, 2019, 28(1): 394-409
[35] FANG Han, JIA Zhaoyang, QIU Yupeng, et al. De-END: decoder-driven watermarking network[J]. IEEE transactions on multimedia, 2023, 25: 7571-7581
- Similar References:
Memo
-
Last Update:
2026-01-05